Official Website:
- Top 5 Hardest Video Game Genres to Develop In 2024Video games provide an immersive experience to players who love to indulge in online fights, …
- 5 Tips for Building a Resilient Cyber Defense For Small BusinessesToday, all businesses, whether big or small, invariably depend on cybersecurity networks for their day-to-day …
- Choosing the Best in Business Networking: Why Automation Solutions Outshine LinkedIn’sIn the realm of business, networking has always been a cornerstone for growth, opportunities, and …
- The Windows File Management 101: Expert Tips for Effective OrganizationOnce upon a time, there were a lot of companies that spent a significant amount …
- Introduction to Home windows XP – Up to dateMicrosoft offered the primary PC working system to IBM in 1981. It was known as …
- Methods on The right way to Repair Home windows Error Code 0x0 0x0Home windows is without doubt one of the most used working methods on the planet. …
- Wifi 5 vs Wifi 6 – Ought to You Improve or Not?Having web connectivity by WiFi might be probably the most essential issues at your house …
- Distinction between WEP, WPA, WPA2, WPA3, WPS WiFi SafetyMost of us had linked to a WiFi community with our laptop computer, pill or …
- What are FTP, SFTP, FTPS & TFTP and their variationsFTP, SFTP, FTPS and TFTP are protocols which are used to switch information over a …
- What is Port ForwardingPort forwarding allows computers over the Internet to connect to a specific computer or service …
- What’s syslogSyslog is a standardized method of manufacturing log info. That is actually widespread in Linux …
- What is SMTP – Simple Mail Transfer ProtocolSMTP stands for a Simple Mail Transfer Protocol. Previously we did an article on POP3 …
- Difference between POP3 and IMAP email protocolPOP3 and IMAP email protocols are used for retrieving email from an email server. For …
- What is a mainframe computerWhen you hear the term “big iron”, this usually refers to mainframe computers, machines that …
- Securing Your PC: How to Choose an Antivirus Software For Windows 10Protecting your PC is something you should definitely prioritize. Fortunately, your Windows 10 PC is …
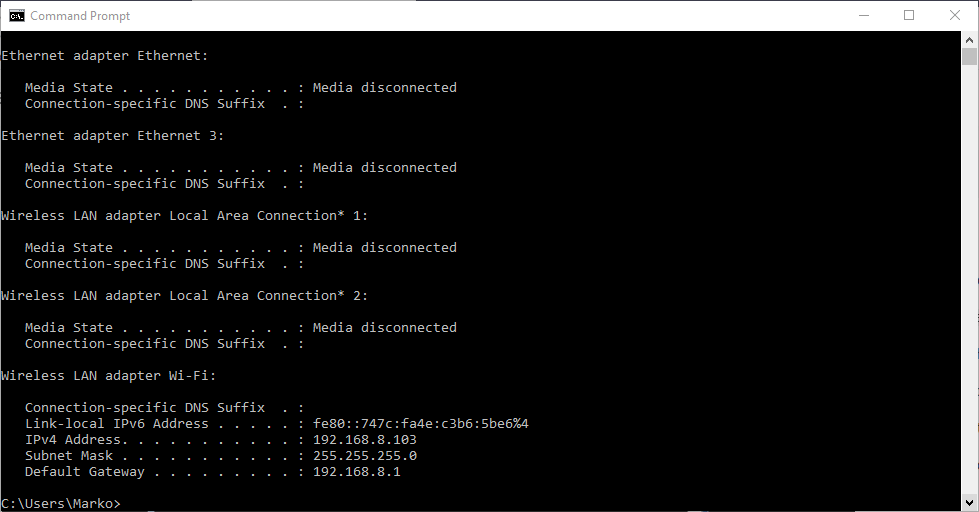
- Network Troubleshooting using PING, TRACERT, IPCONFIG, NSLOOKUP commandsThis article is about a series of network troubleshooting tools that you can use in …
- What is a KernelIf you work with computers, or hang around computers long enough, you might come across …
- HTTP, HTTPS, SSL and TLS ExplainedHTTP stands for Hypertext Transfer Protocol and this is probably the most widely used protocol …
- 6 Issues You Should Do When You Get a New PCBreaking out your new PC is likely one of the most enjoyable emotions on the …
- NTFS, exFAT, FAT32, ext4 File Systems ExplainedFile system is a standard for organizing data on a storage device like a hard …
Check Out More Here > Hire Dedicated Link Building Service